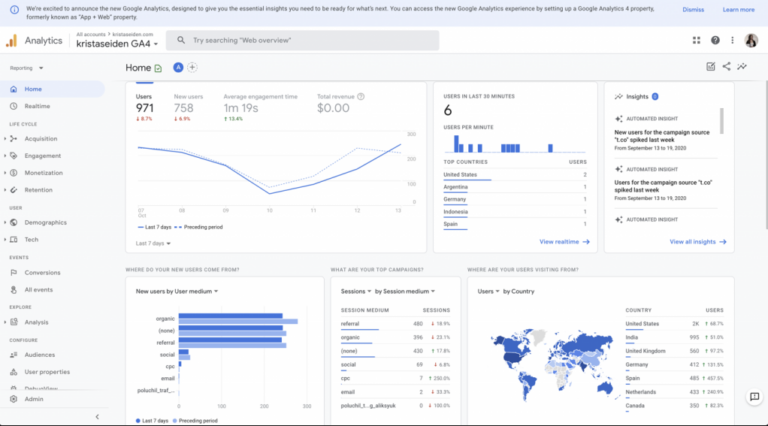
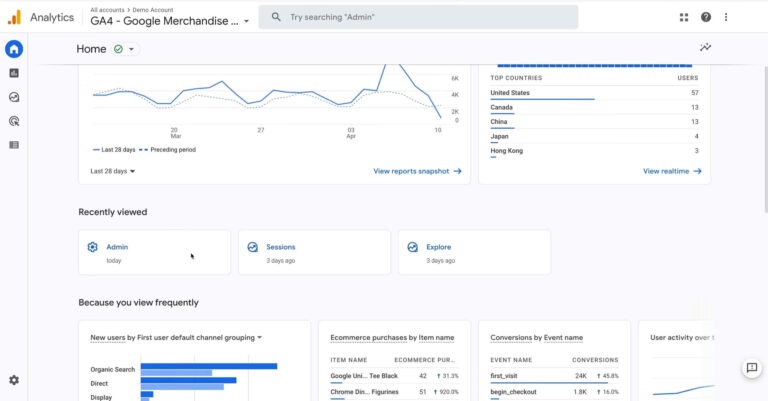
Why Cross-Device Tracking Matters in GA4
Cross-device tracking in Google Analytics 4 (GA4) is a crucial feature that enables businesses to understand the full scope of user interactions across various devices. That capability is essential for providing a comprehensive view of the user experience, optimizing marketing strategies, and improving user experience. Let us talk about it in greater detail. Key Features